For a large client, active in the manufacturing industry, wanted insights in its current IT risk posture.
Summary
As so many organizations, our client, active in the manufacturing industry, wanted insights in its current IT risk posture.
They knew they had too little control over the accounts and their accesses, but had no comprehensive overview of the situation. As a result, they didn’t know exactly what the situation was and where the biggest risks were located. That, in turn, kept them from convincing management to free up resources in order to take action.
To help the client, we performed an in-depth analysis of the key access risks residing in and across their most important applications, and provided them with a report including our findings and recommendations. In just 3 days of work, this enabled them to understand their access risks and gave them objective numbers to support decision-making with regard to next steps.
Approach
-
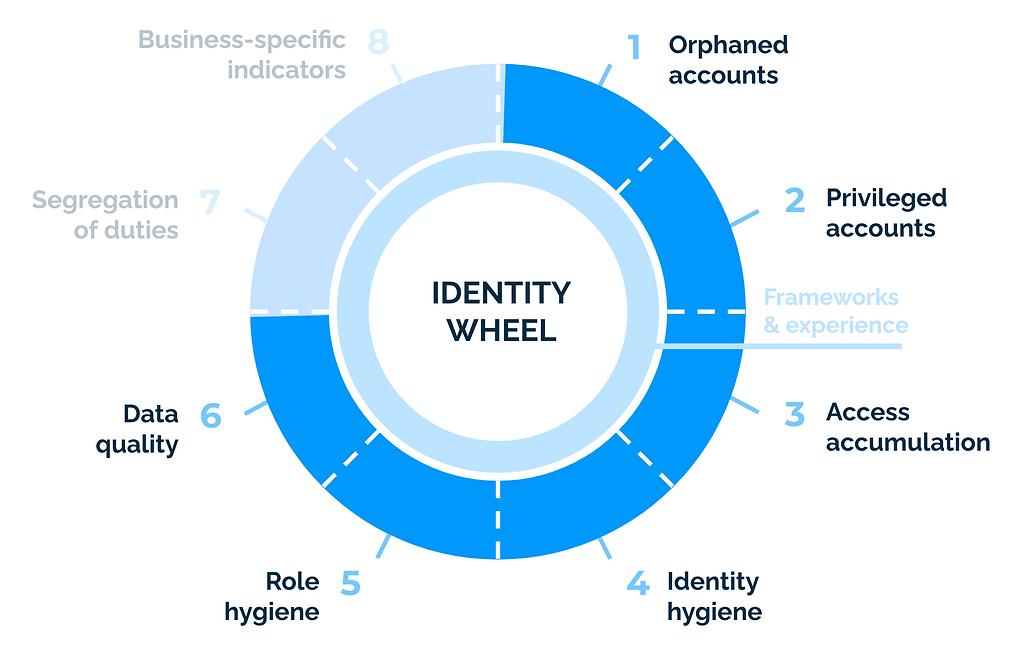
Focus on actual risk: As opposed to typical IAM assessments, we don't focus on the presence of governance processes, but on the actual IT risk present in the existing accounts and their accesses. This allows the customer to prioritize clean-up efforts for maximal risk reduction and efficiently introduce governance processes later on.
4-Step Approach
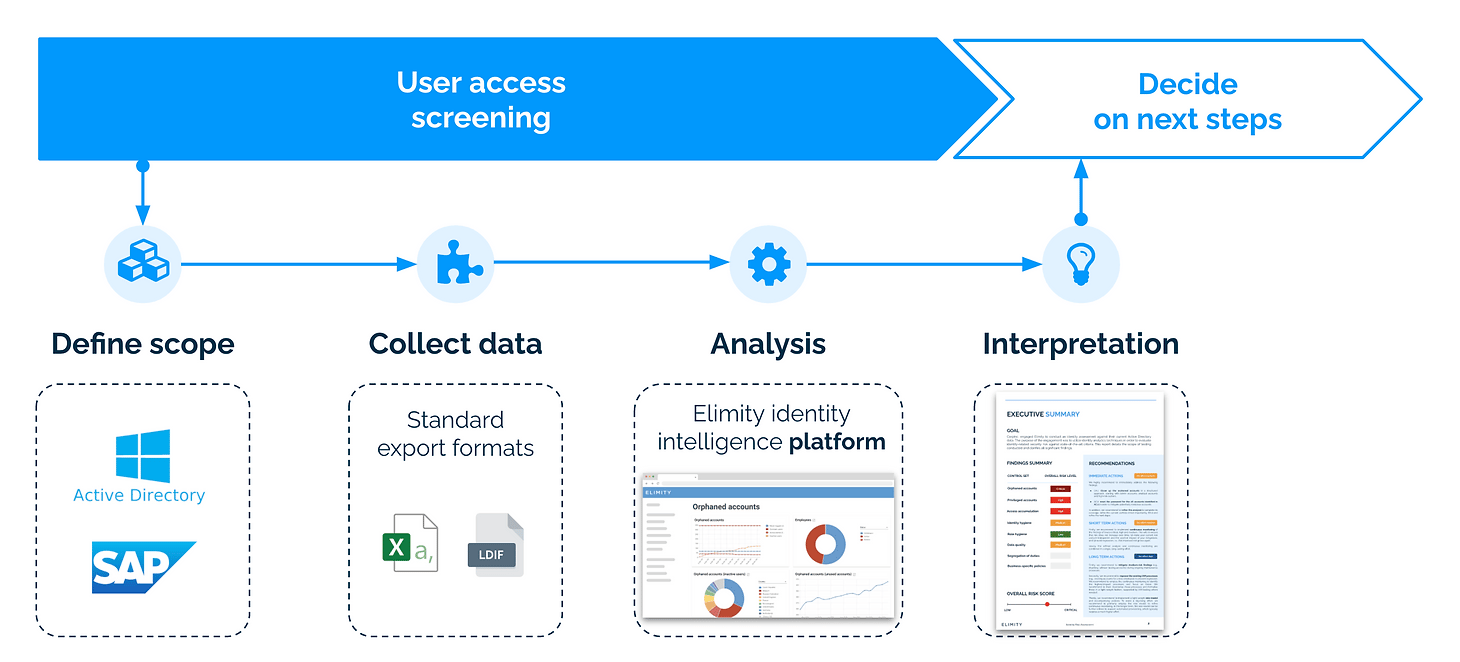
- Define scope: We started with defining the scope of the screening. As our client was particularly concerned about orphaned accounts and their use for attacks such as ransomware, the assessment at least had to cover those applications so that orphaned accounts could be detected. On top of that, we identified the applications where most of the relevant identity data resides. The scope: Active Directory, SAP HR and SAP ERP. They didn’t have a dedicated IAM system yet, otherwise that would have been part of the scope as well.
- Collect data: We then collected and consolidated the relevant identity data from those applications in our platform. To avoid setting up costly data connections specifically for this screening, we quickly imported the data from the standard export formats of these systems (i.e., Excel sheets and CSV files) using our out-of-the-box and custom connectors.
- Analysis: With powerful identity analytics and a comprehensive set of out-of-the-box controls, our platform instantly measures the results for various key access risks (see figure below). For some controls customization took place in terms of modification of some out-of-the-box controls and creation of several new controls specific for their operations.
- Interpretation: Our platform allowed us to dig a little deeper into the results to investigate the inherent risk associated with the findings. This allowed our team of experts to understand the nature of the risks and enabled them to interpret the results and provide recommendations in terms of priorities.
Result
We provided our client with a detailed report of the key access risks in just a couple of daysand gave them access to our platform so they could dig a little deeper into the results themselves.
Impact
Using technology to perform an in-depth analysis gave our client the insights they needed to understand their access risks and enabled them to let others understand them as well.
They used these insights to support the development of the identity roadmap. First stop: clean-up to improve the IT risk posture.